Cyber criminals are abusing even more Tor Network for illegal activities, from botnet management to money laundering, the number of services is increasing.
Tor network is even more used by cyber criminals to cover their illegal activities, the Tor community has observed, for example an alarming increase in the number ofmalware that abuse of the popular anonymizing network to hide their command and control infrastructures.
The coverage of Malware C&C isn’t the unique option for crooks, Tor network could abused also to set up cyber criminal underground forums and black markets.
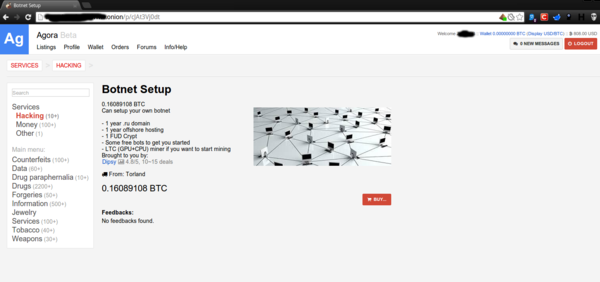
Kaspersky security researcher Sergey Lozhkin published an interesting article on the topic, revealing that Tor network is currently being used to hide C&C server of nearly 900 botnet and other illegal hidden services.
“There are also approximately 5,500 nodes in total and 1,000 exit nodes, but the possibility of creating an anonymous and abuse-free underground forum, market or malware C&C server is attracting more and more criminals to the Tor network.” states the post.
Hiding C&C server is becoming a common practice of malware coders to make theirbotnet more resilient, difficult to trace and decapitate.
Also Zeus malware is migrated in Tor network, at the end of last year security researchers at Kaspersky Lab have detected a 64-bit Zeus banking trojan version enhanced with communication capability on the Tor network.
Early 2014 researchers at RSA discovered a new variant of Tor-based malwareChewBacca that is able to infect Point-of-Sale stealing Credit Card data. Recently it was discovered also the first Android malware abusing of Tor network.
“We expect there will be a rise in new Tor-based malware, as well as Tor support for existing malware,” states the post.
As anticipated, Tor network offers a privileged environment for cyber criminals specialized in the sale of stolen debit/credit card data, numerous carding shops propose stolen personal and necessary products to card frauds (e.g.skimmers, plastics).
“Offers are not limited to credit cards – dumps, skimmers and carding equipment are for sale too,” said the expert.
The offer for carding includes also malware specifically designed to steal credit card data and botnet renting.
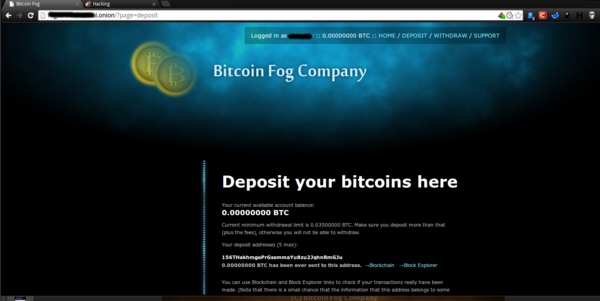
A characteristic of the Tor network is the possibility to pay almost everything withbitcoin, but it is known that it is possible to link a wallet to its owner’ identity and track transactions related to the most valuable transactions made via bitcoinexchange services.
As explained by Lozhkin, money laundering services are also expanding on Tor, the mechanism is simple, cybercriminals use to spread the amount of a single transaction in hundreds /thousands of money transfers through dozens of different wallets making hard to track them.
What about next months?
“A growing number of Tor hidden services and the ease with which they are can be deployed attracts more and more cybercriminals in the Darknet.”
In the next months the number of cyber criminals that will abuse Tor will increase as the number of services available on the anonymizing network.

No comments:
Post a Comment