Chinese researchers from “360 Mobile Security” detected Android Oldboot.B malware, until today the most complexbootkit which infected millions of devices.
A new sophisticated Android Bootkit has been detected by Chinese Security Researchers from “360 Mobile Security“, its name is Oldboot.B and appears as an evolution of its predecessor Oldboot.A. According the researchers Oldboot.B could be considerable as the most sophisticated Android malware ever detected, it has already infected millions of mobile devices. OldBoot.A was detected early 2014 by the Russian security firm Doctor Web, its principal capability is to re-infect the Smartphone after reboot, even if all its components are deleted by the user.Bootkit is a category of malware which infects the host at start-up and it is able to perform malicious activities, including data stealing, disk encryption, communicate with a remote C&C server and remove the application on the victim’s device.‘Oldboot.B‘ implements a new advanced evasion techniques to avoid its detection to principal antivirus software and automatic analysis systems.
“The Oldboot Trojan family is the most significant demonstration of this trend.”“Depending on the commands sent from the C&C server, it can do many different things, such as sending fake SMS messages or phishing attacks, and so on. Driven by profit, the Oldboot Trojan family changes very fast to react to any situation.“ researchers said.
The principal abilities of Oldboot.B trojan are:
- It can install malicious apps silently in the background.
- It can inject malicious modules into system process.
- Prevent malware apps from uninstalling.
- Oldboot.B can modify the browser’s homepage.
- It has ability to uninstall or disable installed Mobile Antivirus softwares.
The Oldboot.B malware, once infected the victim’s Android mobile, waits for the command sent by C&C (located at az.o65.org [IP is 61.160.248.67]), it makes also use of steganography to hide data (executable codes, configuration file) within file exchanged with C&C and installs numerousmalicious applications on the mobile.
“But after some analysis, we found that the configuration of meta_chk is hidden in this picture, which contains the command will be executed by meta_chk and other information.” researchers said. The size of this configuration file is 12,508 bytes.
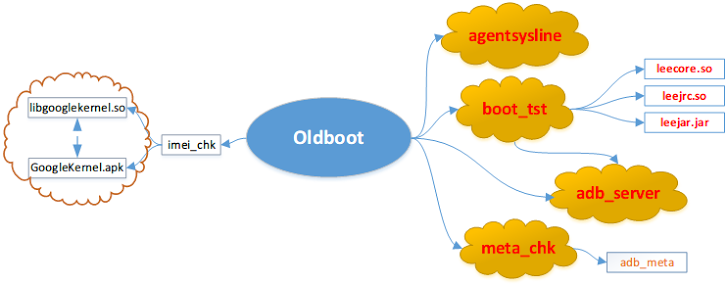
The Oldboot.B malware is composed of 4 principal components that registering itself as services can ensure the persistence to the malicious code.
- boot_tst is the component responsible for command reception and execution. It uses a remote injection technique to inoculate an SO file and a JAR file to the ‘system_server’ process of the Android system.
- adb_server replaces pm script of the Android system with itself, its main functionality is to avoid malicious code uninstall.
- meta_chk silently download and install Android Apps promoted in the background, it is also able to open a backdoor for remote control. The component is able to remove itself leaving injected process in the memory, in this way antivirus software cannot detect it because they are not able to perform a memory scan in the Android platform.
- agentsysline - runs in background receiving commands from C&C server, within its abilities the possibility to delete the specific files, enable/disable network connection and uninstall anti-virus software.
The principal evasion capabilities that make hard the detection of Oldboot.B are:
- It adds some meaningless code and trigger some behavior randomly.
- Check for SIM card availability in the device, and it will not perform certain behavior if there is no SIM card to fool sandbox or emulators.
- Check for the existence of antivirus software, and may uninstall the anti-virus software before doing anything malicious.
The unique possibility to avoid Oldboot.B malware is to download and install app only from official stores neither use untrusted custom ROMs.
If your mobile is infected by Oldboot.B you can download the free removing tool designed by antivirus firm 360 Mobile Security.
No comments:
Post a Comment