Researcher David Kirkpatrick discovered a flaw in older versions of NetSupport Manager could expose sensitive configuration settings and lead to compromise.
A vulnerability in older versions of NetSupport Manager could be a source of serious problems for enterprises that use the platform for remote control of PC and servers. This case is an example of the impact of not updated software on the overall security of the companies. The flaw allows an attacker to access to sensitive configuration settings and information.
The vulnerability was discovered by David Kirkpatrick, a security consultant at Trustwave’s SpiderLabs, which described the flaw in a blog post.
The researcher in a previous research, documented in a blog post, demonstrated how to find versions of NetSupport running on clients with default installations that didn’t require authentication to remotely connect to them. Kirkpatrick wrote a script to exploit NetSupport to bypass any Domain or local credentials to remotely connect to the machine and compromise it, but as remarked by the expert the attacker need access to NetSupport Manager software to run it.
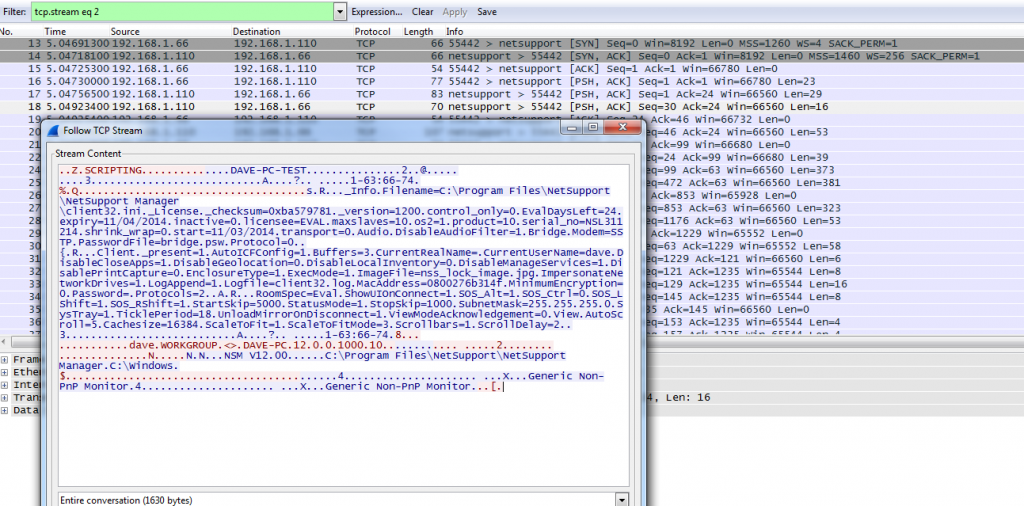
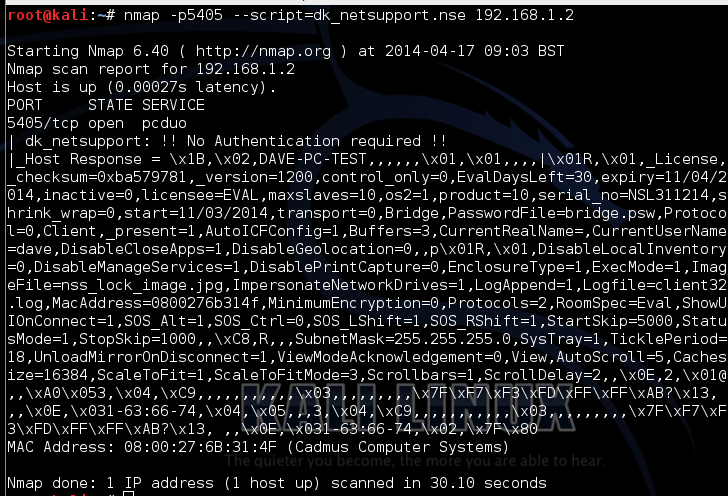
Kirkpatrick has written a simple Nmap script to perform a silent scan searchingvulnerable instance of the software. Kirkpatrick used Wireshark packet analyzer to analyze TCP stream of NetSupport service.
“The ‘Connect’ popup that usually appears on the remote PC, when running the previous NetSupport Manager script, did not pop up when using the Nmapscript after a connection,”“This meant I could run this script across the network and the clients would be unaware of my testing of their configuration.” Kirkpatrick wrote.
Kirkpatrick wrote a specific script to verify if the response includes the word “License”
“If “License” was returned then the information was freely retrieved without authentication. If it wasn’t, that meant that most likely authentication was required to get the results of the query.”“With no information on the NetSupport packet format in my test network, I fired up Wireshark and captured all the relevant data sent from the NetSupport Manager when I performed an Inventory query from the Action menu on the manager to another host, as shown below:” said Kirkpatrick in the post.
The data captured by Kirkpatrick contains the NetSupport version info, hostname, user and the encrypted password of the “Configurator Password.”
Resuming, the step done by the researcher with the NMap script are
- Sends a NetSupport Inventory query in raw packets
- Checks if the response includes the word “License”
- If so, it has successfully connected to the client without the need for authentication
- If not, then most probably it requires authentication
- Displays the response including user information such as hostname, user, version info, password of the “Configurator Password,” etc.
To mitigate the vulnerability in older version it is necessary to change the default setting to enforce password set on clients.
“In this case installing the default NetSupport client settings on a PC, where no Client password is set, can allow information to be freely returned, which can assist an attacker. “
As explained by Kirkpatrick, the flaw in NetSupport software has been fixed in “later revisions.”, version 12 that is currently on the market is secure.
No comments:
Post a Comment